Achieving Zero-Touch Security: Why SSO Isn't Enough for Secure Employee Offboarding
Join hundreds of companies and start your identity governance journey today

The modern enterprise runs on SaaS. The average business now utilizes over 254 different SaaS applications across its ecosystem. While many of these are officially sanctioned and managed by IT, a massive portion operates entirely under the radar. In fact, industry analysts estimate that up to 40% of all IT spending occurs outside the purview of the IT department, a phenomenon known as Shadow IT.
For IT and security teams, managing this sprawling digital footprint is a daily struggle. The biggest risk isn't just knowing what apps exist; it's knowing who has access to them.
This visibility gap becomes critical during employee offboarding. When an employee leaves, every single application they had access to must be deprovisioned on their exit date. A single missed account or orphaned admin credential is low-hanging fruit for attackers and a major liability during compliance audits. Yet, for many IT teams, offboarding remains a manual headache: logging into dozens of individual apps and systems to manually delete access, a process that is notoriously slow, tedious, and highly error-prone.
The "API Gap" in Traditional Identity Management
Technologies like Single Sign-On (SSO) and identity providers, like Microsoft Entra ID, are powerful tools that attempt to consolidate app and access management into a centralized location. They do an excellent job securing a company's core stack.
However, they share a structural dependency: they require a robust API to govern an application.
This creates a massive "API Gap" in the modern IT environment. Many niche SaaS products, internal custom builds, or legacy systems are simply not supported because they lack native API connectors. Even when an API does exist, it often fails to deliver the deep, granular data required to truly take control of the app's permissions.
When your SSO can't reach an app, the governance boundary stops. IT is forced right back to square one: manually logging into disconnected systems or spending months of expensive engineering time performing custom development builds to connect data from system to system.
Achieving Universal Data Integration with Josys
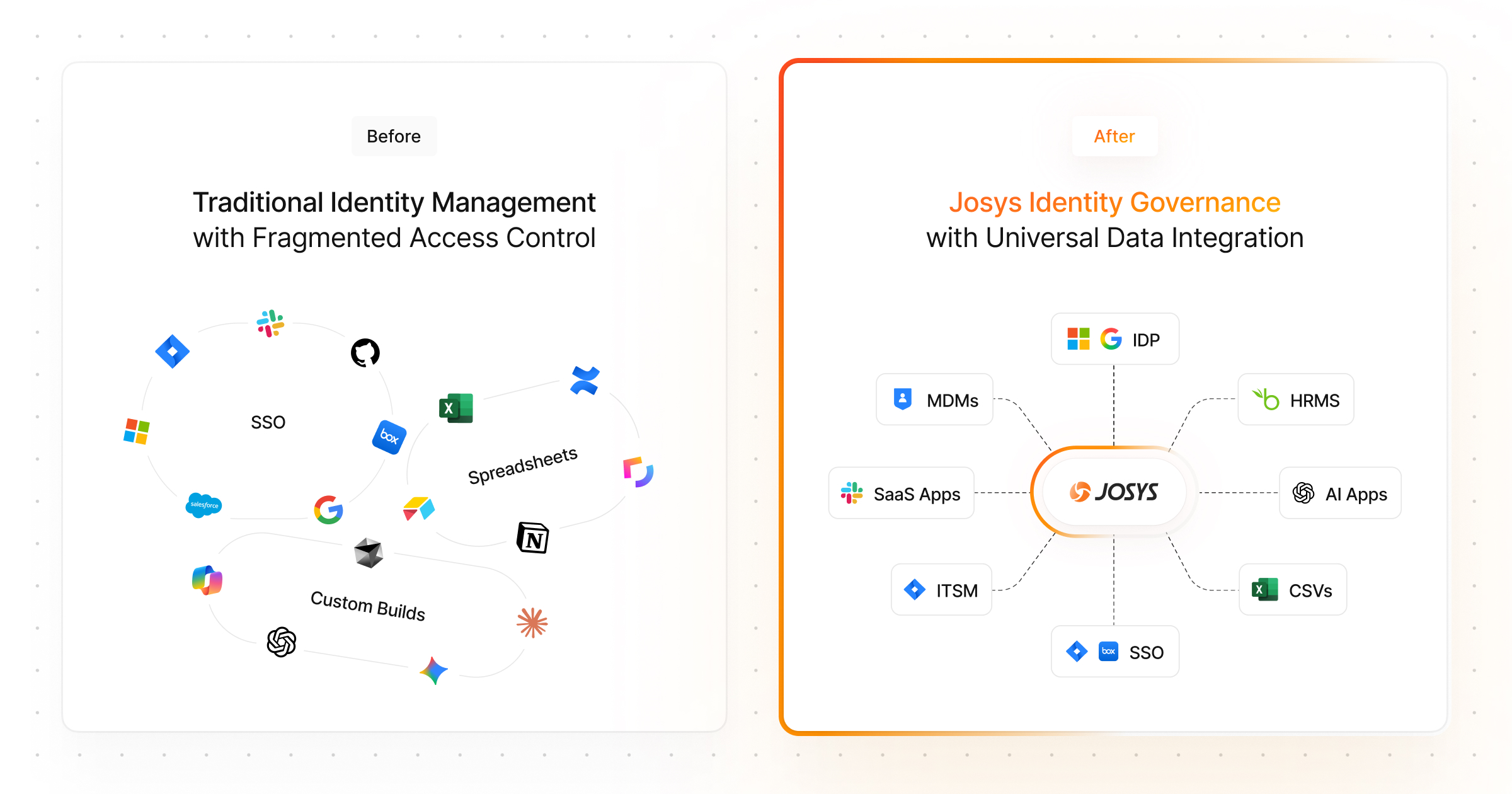
Josys was built to engineer around this exact obstacle by introducing Universal Data Integration.
By leveraging advanced AI, Josys has eliminated the industry’s greatest bottleneck, dependency on APIs, enabling seamless governance across every data source, no matter how legacy or niche.
To solve the API dependency crisis and automate complex lifecycles like offboarding, Josys announced three groundbreaking capabilities in its recent press release:
- AI Integration Builder: For applications with no API at all, Josys has engineered a self-serve AI engine. An IT admin simply records their browser actions while navigating the target app. The system learns the workflow and autonomously extracts user, access, and permission data directly from the application’s UI. The result is total visibility into any custom or unsupported web app in under 30 minutes. No coding or APIs required.
- Multi-Source Identity Enrichment: Effective offboarding requires bridging the gap between HR and IT. Josys combines a primary data source (like Microsoft Entra ID) with a secondary source (like BambooHR). The moment an employee is marked as offboarded in your HR platform, Josys catches the signal and automatically deprovisions their access system-wide.
- Josys App Script: For organizations managing identity data in external systems that fall outside standard connector libraries like Microsoft Entra ID, App Script provides a proprietary framework to quickly build and deploy custom integration scripts. What traditionally takes months of engineering cycles can now be deployed in a matter of days.
Francom Group Closed Offboarding Security Gaps
Even organizations utilizing powerful core identity providers run into the API wall when dealing with niche or custom applications. This leaves IT teams with critical blind spots, especially during sensitive processes like offboarding.
For Francom Group, the Josys AI Integration Builder provided the exact bridge they needed to bypass these limitations and achieve full-environment governance.
"The Josys AI Integration Builder has allowed us to easily integrate and monitor any app, even if it is not supported on Microsoft Entra ID, which is an absolute game-changer for closing the gaps where visibility and offboarding risks usually slip through," said Billy Whiting, System Administrator at Francom Group.
By eliminating the dependency on native API connectors, Francom Group was able to extend their security perimeter to their entire SaaS ecosystem, ensuring no app is left ungoverned and no offboarding step is missed.
Full Coverage, Not Partial Visibility
"Historically, IGA's effectiveness was capped by the scope of its API connectors," says Mahabaleshwar Bhat, Chief Product Officer at Josys. "We are shattering that limitation. By maximizing AI to ingest data from any source, Josys provides the first truly universal governance engine. We are moving from 'connected' IT to 'autonomous' IT, ensuring that no application remains a liability."
The API gap is no longer an accepted limitation; it is an obstacle you can bypass. By centralizing identity data into a single, AI-driven platform, Josys empowers IT teams to transform disjointed environments into scalable, secure operations.
Ready to move from blind spots to autonomous control? Stop logging into individual apps to manage access. Contact us today to book a demo and see Josys in action.
over your identities, applications, and files?
Sign-up for a 14-day free trial and transform your IT operations.














